A notorious group of Russian hackers are claiming to be behind an attack on a Swiss international bank, allegedly stealing customer data and the bank’s source code.
Swiss bank’s data stolen in cyberattack, hackers claim

Listing a company on the ransomware gang’s website is a common tactic used y attackers to force the victims into paying ransom. Normally, it is the first step before publicly releasing the data or selling it if the demands are not met.
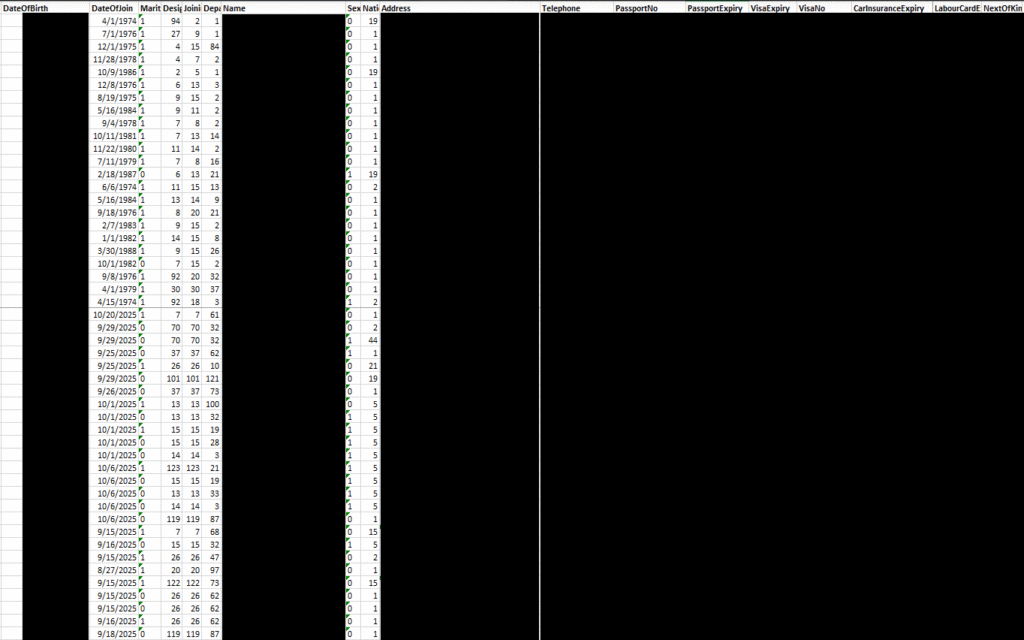
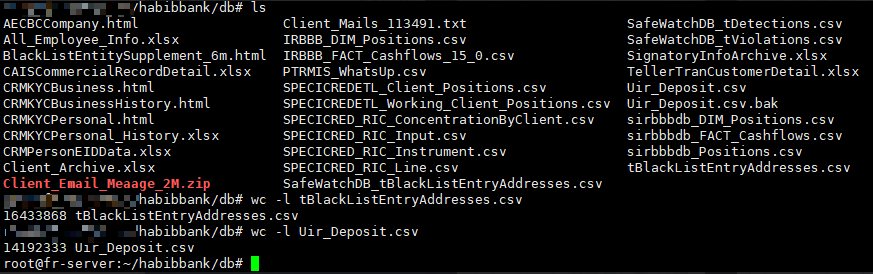
The post, dated November 5th, claimed that the gang had stolen over 2.5 terabytes of data and nearly two million files. To prove its claims, the gang has released screenshots of some of the stolen files, which were investigated by the Cybernews research team.
According to the sample, it seems that the gang managed to exfiltrate a lot of sensitive information from customer accounts, including:

“Due to the broad scope of the potential breach, it is important for Habib Bank to act quickly in order to identify exactly what data was affected, inform affected customers, and audit the stolen source code for potential vulnerabilities, employ stricter monitoring of their servers and other services to detect any further attempted attacks,” our researchers said.
Cybernews reached out to the bank for clarification, but a response has yet to be received.
Founded in 1967, the bank has operations across multiple countries, including Switzerland, the UK, the UAE, Hong Kong, Kenya, South Africa, and Canada. It also has representative offices in Bangladesh, China, Hong Kong, Pakistan, and Turkey.
In 2024, the bank employed a total of 7,904 people across 587 offices and boasted $750 million in revenue.

What is Qilin ransomware?
Qilin is a notable name in the ransomware landscape, known for targeting hospitals and the manufacturing sector.
The Qilin gang first appeared on the ransomware circuit in 2022, but its dark leak site claims that it began operating in 2021. This year, the gang has taken the number one position as the most active ransomware group.
According to Cybernews’ in-house surveillance tool, Ransomlooker, the gang has listed 959 victims since 2023, with many well-known names on the list.
In October, the group claimed to have breached the financial records of two Texas electric power cooperatives, San Bernard Electric and Karnes Electric, exposing sensitive documents. Just last week, Qilin claimed to have exfiltrated data from the large US pharmacy benefit manager, MedImpact.
Qilin ransomware has recently allied with the notorious Russia-linked gang LockBit and DragonForce. Cooperation between the three groups could lead to improved tactics and an increased volume of attacks through the sharing of resources.
Qilin has also claimed an attack on Volkswagen Group France, with the attackers claiming to have exfiltrated about 2,000 files and 150GB of data consisting of sensitive client, employee, and business information.
Previously, Qilin was said to be behind a cyberattack on Asahi Holdings, Japan’s largest brewer. The attack disrupted operations and caused a shortage of the country’s most popular beers, soft drinks, and cold teas.
In August, Nissan’s Creative Box design studio in Tokyo was attacked by the group, which claimed it had stolen 4TB of sensitive design data. The Japanese automaker giant has now confirmed a breach of its network in a public statement.
The gang also claims to be behind a breach of the California Golf Club of San Francisco, considered one of the nation’s most exclusive members-only golf clubs, and a favorite of Silicon Valley execs. The gang allegedly stole 10GB of its members’ data.
The gang is behind the infamous attack on NHS partner Synnovis Laboratories. The attack had devastating consequences, as hospitals were immediately forced to divert patients to other facilities and cancel over 10,000 appointments, elective procedures, and surgical operations, including all transplant surgeries, due to a lack of blood transfusions.
Qilin has carved its name into this year’s hall of fame for devastating cyberattacks by claiming the South Korean telecommunications giant SK Telecom. The attackers claimed to have stolen 1TB of data.
After a public apology from SK Telecom CEO Yoo Young-sang, the company was forced to offer free SIM card replacements to all its customers in the aftermath, and said it would “continue to implement ‘double and triple’ safety measures until the concerns and worries of customers were resolved.”
To accommodate the swap, the company had to halt new sign-ups until it had changed SIM cards for those affected by the cyberattack